Latest Version
Software Name
Ad-Aware Web CompanionSoftware Version
1.1.908.1803Price
FreeFile Size
7.7 MB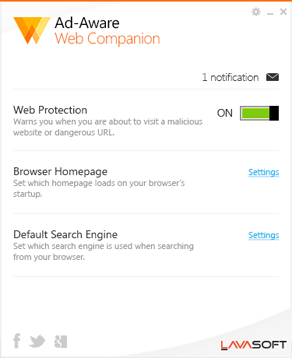
Ad-Aware Web Companion Security Bulletin
A great deal of attention has been given to recent events surrounding Superfish and Lenovo, and the resulting security vulnerability that has been exposed in Komodia, an independent sub-component of Superfish’s product.
Lavasoft takes security issues very seriously, and would like to take a moment to explain to our users who are naturally concerned by the overlap between Lavasoft and Komodia.
Komodia delivers a collection of utility SDKs for scanning and intercepting internet traffic on a user’s PC. Applications using Komodia SDKs can be quite useful such as parental control software or security products like Ad-Aware Web Companion. Unfortunately, Komodia components can also be used to inject advertisement on third party websites through products like Superfish.
One of the technologies used by Komodia to inspect HTTPS (SSL-encrypted) web traffic is a root CA certificate. Recently, it was discovered that the root CA certificate it uses was compromised, creating a security vulnerability that can be exploited.
For the past year, Lavasoft has been developing and testing a new security feature in Ad-Aware Web Companion to scan and eliminate malicious content/advertising in HTTPS traffic, including content injected by Internet proxies and adware installed on the PC. This functionality was implemented using Komodia’s “SSL Digestor” SDK, which includes the aforementioned root CA certificate. At no point was any encrypted information collected or analyzed.
Prior to the public announcement of the security vulnerability, and upon consultation with our partners and evaluation of the risks/benefits to our end-users, Lavasoft took the decision to remove the functionality and eliminate the deployment of the root CA certificate to inspect traffic.
Although Lavasoft’s most recent release of Ad-Aware Web Companion (released on February 18th 2015) removed this functionality and was not supposed to contain the SSL Digestor; it was determined that trace elements of the Komodia SSL Digestor were still present.
These remaining elements have since been removed and we recommend that all users update to the latest release of Web Companion using the link on this page. All existing end-users using are being notified of the update via the product.
Update March 3rd 2015: Firefox users no longer need to uninstall to patch this vulnerability. A simple update will correct this issue. If you are experiencing any difficulties with updating to the latest version of Ad-Aware Web Companion, you will need to uninstall and re-install the software.
Important note: Firefox users will need to uninstall and re-install Ad-Aware Web Companion in order to patch this vulnerability. No other Lavasoft products leverage Komodia, with one exception; Ad-Aware AdBlocker (alpha) 1.3.69.1, the unreleased predecessor of Web Companion is also affected by this vulnerability. It is an unsupported product. Alpha testers who have not uninstalled it by now are instructed to do so immediately, and to manually check to ensure the root CA certificate has been deleted as we cannot guarantee the integrity of the uninstaller in this pre-released version.
We thank you for your patience and your understanding.
Last updated: March 03, 2015.